
A well-designed casino platform architecture must do four things simultaneously: handle traffic spikes without service degradation, keep every wallet transaction provably accurate, maintain clear audit records for regulators, and allow individual services to be updated or scaled without touching the whole system. Getting this wrong has a direct cost — a wallet error during peak traffic is a regulatory incident, not just a bug, and a poorly architected platform rebuilds rather than scales.
This guide covers the practical architecture for a scalable casino platform — from service boundaries and wallet design to compliance workflows, observability, and safe release practices. It is written for developers, CTOs, and product leads at operators and studios building or re-platforming a casino product. For game-level architecture specifics, see our related guides on casino game architecture components and low-latency casino game optimisation.
Scope of this guide: This covers the platform layer — identity, wallet, compliance, payments, integrations, observability, and infrastructure. It is not a guide to individual game mechanics or casino game server architecture (see the related links above). The platform is what sits between your games and your players, and between your business and your regulators.
What "scalable" means in a casino platform architecture

In casino systems, scalability means more than handling more users. It means three things working together: traffic scalability (more concurrent sessions without latency increase), money safety at scale (wallet accuracy that does not degrade under parallel load), and operational scalability (the ability to deploy changes, run compliance checks, and respond to incidents without taking the platform down).
Most casino platforms that fail under load do not fail because their servers run out of CPU. They fail because a service boundary was drawn incorrectly — usually wallet logic mixed with game session logic, or compliance checks blocking the bet confirmation path. The architecture decisions that matter most are made before a single line of code is written.
- Horizontal vs vertical scaling: Stateless services (API gateway, game session handlers, compliance check endpoints) scale horizontally — add instances. Stateful services (wallet ledger, player account store) scale through read replicas, sharding, and caching layers — not by adding instances of the write path.
- Service isolation: A slow reporting query should never delay a bet confirmation. A failing fraud check should not block a deposit. Every service that is not on the critical path for money movement must be isolated from that path architecturally — not just by SLA.
- Correctness before performance: Every optimisation that trades accuracy for speed in the wallet layer should be refused. A 10ms improvement that introduces a 0.001% chance of a ledger discrepancy is not a trade-off — it is a compliance incident waiting to happen.
A scalable casino platform architecture — service layer design

A clean platform architecture keeps each layer focused on one responsibility. That makes individual services easier to scale, update, and troubleshoot without side effects on the rest of the system.
PostgreSQL for account records, Redis for session token cache, JWT or opaque tokens with short TTL.PostgreSQL with row-level locking, event sourcing pattern for ledger, Redis for balance cache with write-through.Redis for active session state, Kafka for round-completion events to wallet, PostgreSQL for completed round archive.RabbitMQ or Kafka for async processing, PostgreSQL for transaction ledger, idempotency keys on every payment event.Kafka events, synchronous checks on account creation and withdrawal. Dedicated compliance DB with immutable event log.Kafka stream from wallet/session events → ClickHouse or BigQuery for OLAP. Never run reports on the OLTP wallet DB.RNG, fairness, and certification in casino platform architecture
Casino platforms must prove that outcomes are fair and auditable. Keep RNG and game logic strictly on the backend — the client must never be able to predict or influence outcomes. This is not just a security requirement; it is a licensing requirement in every regulated jurisdiction.
- Server-side RNG: All random number generation runs on the server. The client receives outcomes, not seeds. Use a cryptographically secure PRNG (e.g.,
ChaCha20or hardware-sourced entropy via/dev/urandom). Log the seed, input parameters, and output for every round. - Audit trail design: Store round inputs, outputs, timestamps, player ID, wallet transaction reference, and RNG version in an immutable append-only log. The log must be reproducible — given the same seed and inputs, the platform must produce the same output. This is a prerequisite for dispute resolution and licensing audits.
- Versioned RNG: When updating RNG logic (including bug fixes), version the change. In-flight rounds must complete under the version that started them. Regulators expect the ability to reproduce any historical outcome — this requires version tagging on every round record.
- Certification support: Testing laboratories (eCOGRA, BMM, GLI) require access to your RNG implementation and audit logs. Build your audit log export before you apply for certification — retrofitting it is significantly more expensive than building it correctly initially.
Real-time gameplay and session state in a scalable casino platform

Many casino platform architectures fail because they treat every feature as real-time. In practice, only a narrow path needs sub-100ms response times. The most impactful architectural decision in session management is separating what must be fast from what can be deferred.
Critical rule: Keep wallet and payment logic strictly transactional and off the fast path. Money events must be confirmed through durable systems (a confirmed DB write with an ack), not streamed like live UI updates. A wallet credit acknowledged via WebSocket before the DB write completes is a race condition — and in a casino context, a regulatory incident.
WebSocket vs polling vs HTTP for session events
Use WebSocket for live dealer tables, in-play game state, and real-time balance updates. For RNG slots and table games, a request-response model over HTTPS is architecturally simpler and easier to audit. Not every game needs a persistent connection — establish WebSocket connections selectively based on game type, not as a default.
Data design for a scalable casino platform — wallet safety and analytics separation
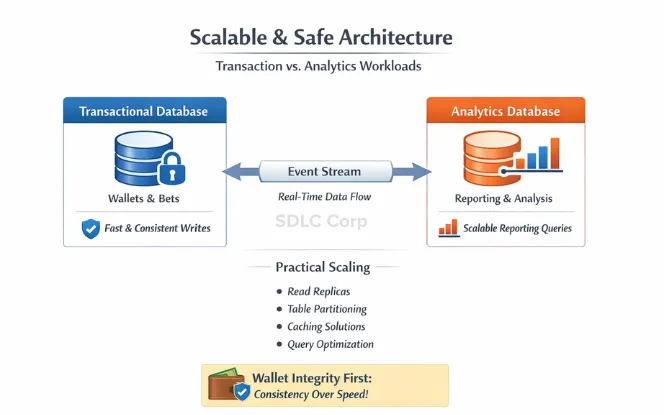
The most common casino platform data failure is running analytical queries on the same database that handles wallet writes. A poorly structured reporting query during peak traffic can cause wallet write latency to spike by 10–50×. This is not a performance issue — it is a correctness risk, because delayed wallet writes during high-load periods create reconciliation problems.
Transactional layer (wallet, accounts, sessions)
- PostgreSQL for wallet and ledger — ACID compliance, row-level locking, and mature tooling for financial data. Use
SELECT FOR UPDATEon balance rows during bet processing to prevent race conditions. - Append-only ledger pattern: Never update a wallet balance record. Instead, append a credit or debit event and derive the current balance from the event sum. This gives you a complete audit trail and makes reconciliation straightforward.
- Idempotency keys on every write: Every deposit, withdrawal, bet, and win must carry a unique idempotency key. Duplicate payment callbacks (a common occurrence with PSPs) must be detectable and safely ignored without double-crediting.
Analytical layer (reporting, compliance, BI)
- Stream wallet and session events to a separate analytical store via Kafka or AWS Kinesis. The analytical DB is a replica, not the source of truth.
- Use ClickHouse for regulatory reporting (sub-second aggregations on hundreds of millions of events), BigQuery or Redshift for BI and player behaviour analytics.
- Reporting jobs — GGR reports, player activity reports, AML threshold exports — run against the analytical store. They never touch the transactional wallet DB.
Practical scaling techniques
- Read replicas for account lookups, game catalog queries, and balance display requests. Replicas can lag by 100–500ms — this is acceptable for display purposes but never for wallet write validation.
- Partitioning high-volume tables (bet history, round log) by date. Queries on historical data hit only the relevant partition. New writes land on the current partition only.
- Redis for balance caching with write-through invalidation. The cache is a performance optimisation — the wallet DB is the source of truth. Cache reads must be validated against the DB on any discrepancy.
Payment integrations in scalable casino platform architecture
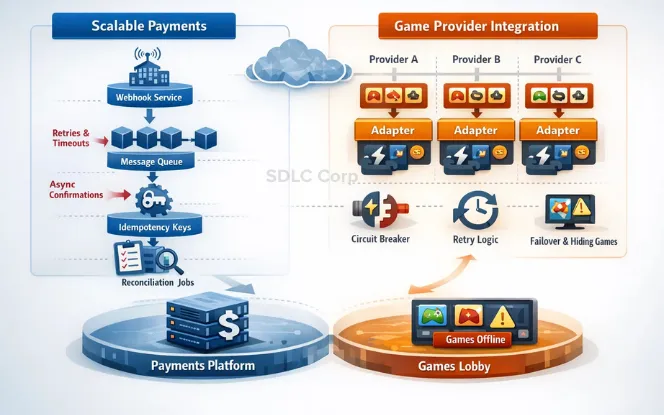
Payment workflow design
Deposits, withdrawals, and PSP callbacks are workflows, not single requests. A deposit involves the player initiating, the PSP processing, a callback arriving at your platform, wallet crediting, and a reconciliation check. Any step can fail or be delayed. The platform must handle this gracefully.
- Webhook-first ingestion: Receive PSP callbacks via a dedicated webhook endpoint that writes to a queue immediately and returns
200 OK. Processing happens asynchronously — the webhook endpoint is never blocked by wallet logic. - Queue-based processing: Payment events flow through a RabbitMQ or Kafka queue. Workers process them with retry logic and exponential backoff. A payment that cannot be processed is dead-lettered for manual review, not silently dropped.
- Idempotency on callbacks: PSPs retry failed webhook deliveries. Your callback handler must detect and safely reject duplicate event deliveries. Use the PSP's transaction ID as your idempotency key, stored in a deduplication table with a TTL.
- Reconciliation jobs: Run daily reconciliation comparing your internal ledger against PSP settlement reports. Discrepancies trigger alerts — they are not investigated manually at month-end.
Game provider integration
Provider connections should absorb provider instability instead of propagating it to players. Each provider needs a dedicated adapter that enforces consistent timeouts, retries safely, and implements a circuit breaker.
- One adapter per provider: Never build a generic provider adapter. Provider APIs differ significantly in timeout behaviour, error codes, and retry safety. A shared adapter that handles all providers produces subtle bugs when one provider behaves unexpectedly.
- Circuit breaker pattern: If a provider returns errors above a threshold rate, the circuit opens — that provider's games are hidden from the lobby and players are not routed to it. The circuit closes automatically when the provider recovers. This prevents a single failing provider from degrading the overall platform.
- Timeout enforcement: Set explicit timeouts on all provider calls (typically 3–5 seconds for game launch, 1–2 seconds for round result). A provider that hangs indefinitely must not hold a player session thread open.
Compliance workflows in casino platform architecture — UKGC and MGA technical requirements
Compliance is not one integration. It is a group of workflows that must remain enforceable during high traffic, provider failures, and routine maintenance. A compliance check that is bypassed during peak load is not just a bug — it is a licensing violation.
Architecture principle: The client can request an action. The platform decides what is allowed and logs why each decision was made. A player claiming they have not hit their deposit limit is not evidence — the platform's log is. Design every compliance decision as a logged server-side verdict, not a client-side assertion.
Performance architecture — load balancing, caching, and CDN for casino platforms
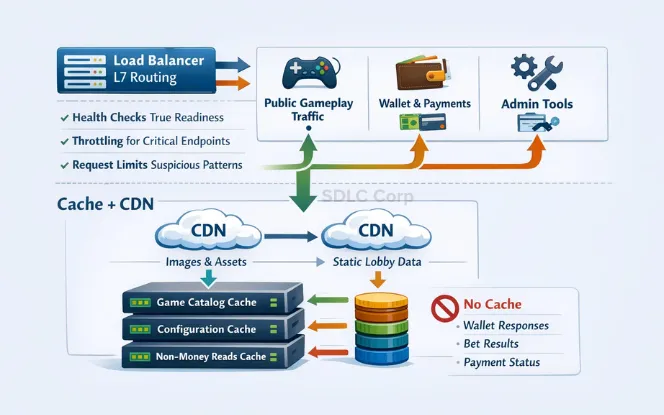
Load balancing strategy
Use layer 7 (HTTP) load balancing to separate traffic categories. Public gameplay traffic, wallet and payment APIs, and admin tools must be on separate load balancer rules — a DDoS targeting the lobby should not affect the payment API, and a slow admin query should never compete with bet placement.
- Health check configuration: Readiness-based health checks — a server is only in rotation when it has confirmed DB connectivity and can process requests. Liveness checks alone miss the case where a server is alive but its dependencies are down.
- Rate limiting per endpoint class: Wallet and payment endpoints have strict rate limits (typically 10–50 requests/second per player). Game launch and catalog endpoints have higher limits. Admin endpoints have IP-restricted access. Never apply uniform rate limits across endpoint classes.
- Sticky sessions for live games: Live dealer tables require session affinity — a player must be routed to the same server instance throughout a session. Use consistent hashing on player ID for routing, with failover to a new instance on health check failure.
Caching and CDN
| Resource | Cache strategy | TTL | Invalidation |
|---|---|---|---|
| Game catalog & metadata | CDN + Redis | 15 min | On provider update event |
| Game assets (JS, CSS, images) | CDN with fingerprint | 1 year (immutable) | Deploy new filename |
| Player balance display | Redis write-through | 5 sec | On every wallet write |
| KYC / account status | In-memory per session | Session TTL | On status change event |
| Wallet write responses | Never cached | — | — |
| Bet results | Never cached | — | — |
| Payment status | Never cached | — | — |
Reliability and disaster recovery in casino platform architecture

Scalability without reliability creates risk. A platform that can handle 100,000 concurrent users but cannot recover from a zone failure within 5 minutes is not production-ready for a regulated market.
- Multi-zone deployment: Core services (wallet, identity, payments) must run across at least two availability zones. A single zone failure should not cause player-visible downtime. Use active-active where possible — active-passive adds recovery time that regulated markets may not accept.
- Automatic failover with SLA commitment: RTO (Recovery Time Objective) for wallet services: under 60 seconds. RPO (Recovery Point Objective): zero — no committed wallet transactions should be lost. These targets must be in your architecture from day one, not added as a retrofit.
- Graceful degradation: Non-critical services can degrade under load without affecting money movement. If reporting is slow, queue it. If a game provider is failing, disable that provider's games. If fraud checks are overloaded, apply stricter automatic rules rather than disabling the check entirely.
- Backup and restore testing: Automated daily backups are table stakes. Restore testing — actually restoring from backup and validating data integrity — must be a scheduled exercise, not an emergency-only procedure. Run a full restore drill quarterly minimum.
- Chaos engineering: Intentionally fail individual services in a staging environment to validate that the platform degrades correctly and recovers automatically. A casino platform that has never had a simulated zone failure will respond unpredictably to a real one.
Security foundations for casino platform architecture
- TLS everywhere: All traffic in transit encrypted. Internal service-to-service communication (often overlooked) must also use TLS. A compromised internal service that can read plaintext bet traffic is a regulatory exposure.
- Encryption at rest: Wallet data, player PII, and payment details encrypted at rest. Use your cloud provider's KMS (AWS KMS, Google Cloud KMS) with key rotation policies aligned to your licensing authority's requirements.
- Secrets management: No credentials in environment variables, config files, or source code. Use HashiCorp Vault or your cloud provider's secrets manager. Rotate credentials automatically; audit every credential access.
- Role-based access control: Principle of least privilege on every service. Game session handlers cannot read wallet records. Reporting services cannot write to any operational table. Enforce at the database level, not just the application level.
- Immutable audit logs: Audit logs for money events, compliance decisions, and admin actions must be tamper-evident. Write to an append-only store (e.g., AWS CloudTrail, or a write-once S3 bucket with Object Lock) that the application cannot modify or delete.
Observability for casino platform architecture — catching incidents before players do

Treat observability as a core feature — not an operational afterthought. The difference between a casino platform with good observability and one without is the difference between catching a wallet processing delay at 30 seconds and discovering it via player support tickets at 30 minutes.
Metrics that matter for casino platforms
- Wallet write latency P95 and P99: Not just average. The P99 is what your slowest 1% of players experience — in a casino, that is the moment they are deciding whether to deposit more.
- Payment callback processing lag: Time from PSP callback received to wallet credit confirmed. Alert at 30 seconds, escalate at 2 minutes.
- RNG service availability: Any gap in RNG availability is a game outage. Monitor with 5-second resolution.
- Compliance check failure rate: If KYC or AML checks are failing silently, you may be allowing transactions that should be blocked. Alert immediately on error rate above 0.1%.
- Queue depth for async jobs: A growing queue depth for payment processing or bonus crediting indicates a worker bottleneck before it becomes a player problem.
- Reconciliation discrepancy count: Should be zero. A non-zero count from the daily reconciliation job is a P1 incident, not a morning metric to review.
Tooling
Use Prometheus + Grafana for metrics and dashboards, OpenTelemetry for distributed tracing across service boundaries, ELK stack (Elasticsearch, Logstash, Kibana) or Datadog for log aggregation. Structured logging (JSON format with consistent field names) is mandatory — unstructured logs cannot be queried reliably under incident pressure.
Safe releases for casino platforms — deploying without breaking money flows
Casino platforms need regular updates, but wallet and payment flows cannot break during a release. The deployment strategy that matters most is how you handle the transition between versions when active sessions and in-flight payment callbacks exist.
- Blue-green deployments: Maintain two identical environments (blue = current production, green = new version). Switch traffic atomically. Rollback is instant — flip back to blue. Required for any wallet service update.
- Canary releases for non-wallet services: Route 5% of traffic to the new version. Monitor error rate, latency, and compliance check pass rate for 30 minutes before promoting to 100%.
- Feature flags: New compliance checks, new game integrations, and new payment methods behind feature flags. Enable for internal users first, then by player segment, then fully. A compliance change that behaves unexpectedly can be disabled in under 60 seconds.
- Backward-compatible DB migrations: Never deploy a DB migration that removes a column or changes a data type without a transition period. Old code must be able to read new data, and new code must handle old data, for at least one deployment cycle.
- Automated smoke tests on every deployment: A full bet flow test (login → game launch → bet → settlement → balance check) runs automatically after every deployment. Deployment fails if smoke test fails.
Casino platform architecture by scale tier
- Modular monolith with clear service boundaries
- Single PostgreSQL with read replica
- Redis for session and balance cache
- RabbitMQ for async jobs
- Single-region, multi-zone
- CDN for static assets
- Extract wallet + payments as independent services
- Kafka for event streaming
- Separate analytics DB (ClickHouse)
- Horizontal autoscaling on stateless services
- Multi-region active-active for wallet
- Dedicated compliance service
- Full microservices with independent deployment
- DB sharding on wallet ledger
- Global CDN with regional PoPs
- Dedicated fraud ML pipeline
- Multi-region with geo-routing
- Chaos engineering programme
Pre-launch checklist for casino platform architecture
Build a casino platform that scales safely
SDLC Corp designs and delivers iGaming platform architecture — wallet systems, compliance integrations, payment pipelines, and observability infrastructure for operators launching or re-platforming casino products. See our iGaming software development services.
FAQs — Casino platform architecture
What is a scalable casino platform architecture?
A scalable casino platform architecture is a backend and infrastructure design that handles increasing player counts, transaction volumes, and traffic without degrading wallet accuracy, compliance enforcement, or game availability. It typically consists of separate services for identity, wallet and ledger, game sessions, payments, compliance, and analytics — each scaled independently based on its load profile. See our guide to casino game architecture components for game-level detail.
What are the most important services in casino platform architecture?
The critical services are: identity and account management, wallet and ledger (the most important — must be ACID-compliant and never share its DB with analytical workloads), game session management with server-side RNG, payment workflow processing, compliance and risk controls (KYC, AML, responsible gambling), and observability. The wallet service is architecturally the most consequential — errors there are regulatory incidents, not bugs.
How should I structure a casino platform for scale?
Start with a modular monolith with clear service boundaries at launch (up to ~5,000 CCU). Extract the wallet and payment services as independent deployments at the growth tier (5,000–50,000 CCU). Move to full independent microservices with Kafka-based event streaming at scale tier (50,000+ CCU). The critical mistake is jumping to microservices too early — the operational overhead requires a team and tooling that most platforms cannot sustain at launch scale.
How does cloud autoscaling help casino platforms?
Autoscaling helps stateless services — API gateways, game session handlers, compliance check endpoints — absorb traffic spikes without pre-provisioning. It does not help the wallet write path, which scales through sharding, read replicas, and caching rather than adding write instances. CDN autoscaling handles static asset delivery (game assets, lobby resources) and reduces origin server load significantly — typically 80–90% of static requests are served from CDN edge nodes, not your origin.
How do you deploy updates to a casino platform without downtime?
Use blue-green deployments for wallet and payment services — maintain two identical production environments and switch traffic atomically. Use canary releases for non-wallet services — route 5% of traffic to the new version, monitor for 30 minutes, then promote. All database migrations must be backward-compatible for at least one deployment cycle. Every deployment must run automated smoke tests (a full bet flow from login to settlement) before going live.
What compliance controls must casino platform architecture enforce server-side?
All of them. KYC status gating on deposits and withdrawals, GAMSTOP/self-exclusion checks on account creation, deposit and loss limit enforcement, AML transaction monitoring, and geo-blocking by jurisdiction must all be enforced at the backend. The client can request an action — the platform decides what is allowed. Any compliance control enforced only at the client layer is not a compliance control; it is a suggestion.
















